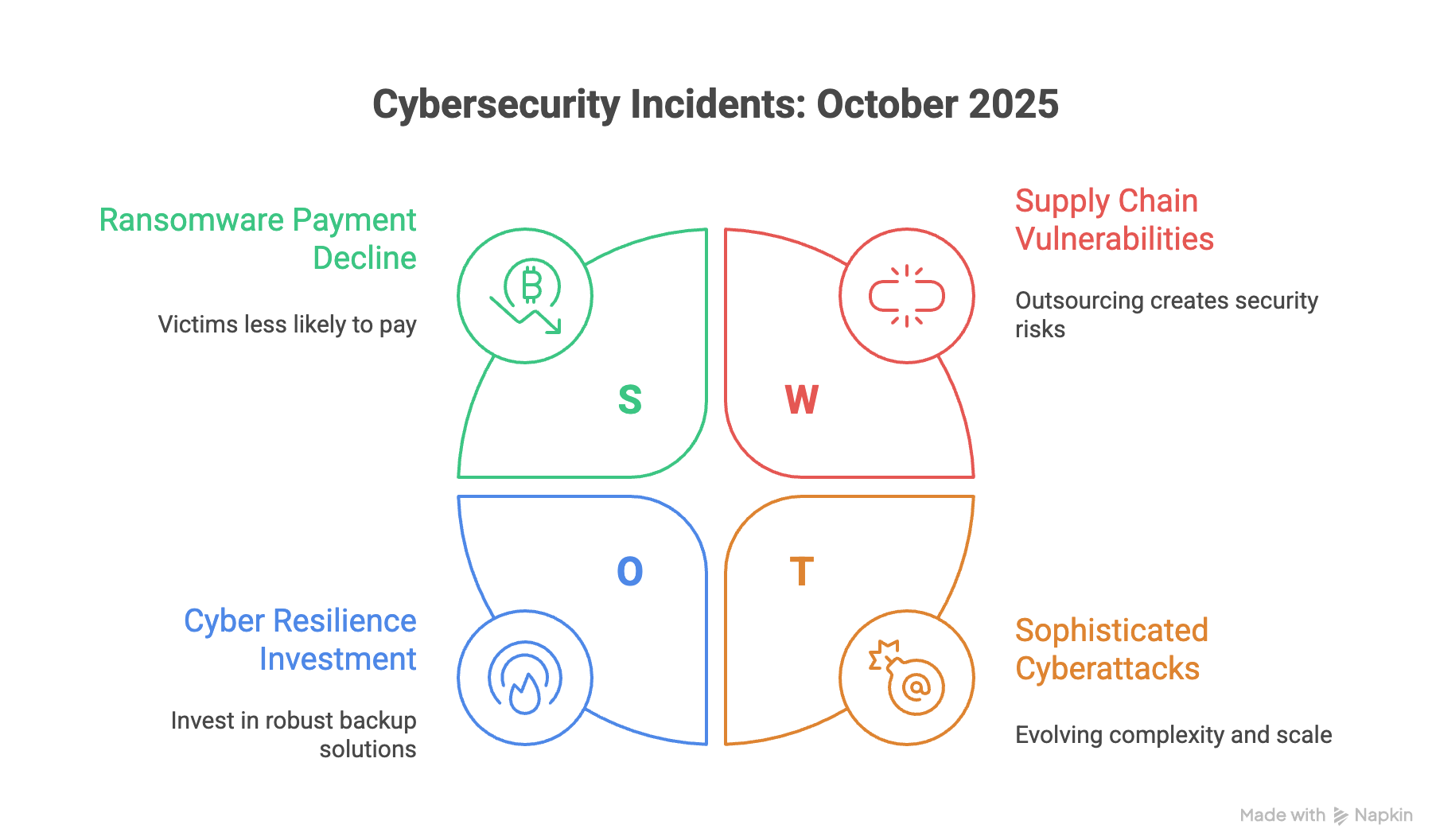
October 2025 was a turbulent month in the world of cybersecurity, with nation-state actors, sophisticated ransomware gangs, and critical zero-day vulnerabilities dominating the headlines. From emergency directives issued by CISA to massive data breaches affecting millions, the threats facing organizations continue to evolve in complexity and scale. This monthly roundup from Cyber Grants Alliance provides a summary of the top 10 most important cybersecurity incidents and what they mean for your industry.
The first step in cybersecurity is to understand your organization’s security risks. We strongly recommend running a Cyber Penetration Test to identify and mitigate vulnerabilities before they can be exploited.
A nation-state affiliated cyber threat actor compromised F5 systems, exfiltrating proprietary source code and vulnerability information. This prompted CISA to issue an emergency directive for federal agencies to immediately patch F5 BIG-IP devices. The attackers now have a significant advantage in exploiting these widely used networking products.
Organizations in financial services, healthcare, telecommunications, and government contracting are at high risk, as they heavily rely on F5 infrastructure for critical operations. Any business with public-facing F5 management interfaces should consider this a critical threat.
A high-severity privilege escalation vulnerability in VMware Tools and VMware Aria Operations (CVE-2025-41244) was actively exploited by a China-linked threat actor for nearly a year before being patched. The flaw allows attackers to gain root-level access on virtual machines, posing a severe risk to virtualized environments.
Data centers, cloud service providers, and enterprise IT departments are at critical risk. Any organization using VMware virtualization should prioritize patching immediately to prevent attackers from gaining complete control over their virtual infrastructure.
Business process outsourcing (BPO) giant Conduent confirmed a massive data breach from 2024 that exposed the sensitive personal information of over 10.5 million individuals. This incident highlights the significant supply chain risks associated with outsourcing business functions.
Healthcare organizations, government agencies, and insurance companies that use BPO services are most vulnerable. This breach underscores the need for robust vendor risk management programs to ensure third-party partners have adequate security controls.
The Qilin ransomware gang has developed a sophisticated technique to execute Linux-based encryptors on Windows systems by using the Windows Subsystem for Linux (WSL). This allows the malware to evade many traditional security tools that are not configured to monitor WSL activities.
Technology companies, software development firms, and financial institutions with hybrid Windows/Linux environments are particularly vulnerable. Organizations with WSL enabled should implement enhanced monitoring to detect this advanced evasion tactic.
The Clop ransomware gang launched a widespread extortion campaign by exploiting a zero-day vulnerability in Oracle E-Business Suite (EBS). The attackers stole sensitive data from unpatched systems and sent extortion emails to executives, demonstrating the severe financial and reputational risks of delayed patching.
Manufacturing, retail, and professional services firms that rely on Oracle EBS for enterprise resource planning (ERP) are at high risk. This incident serves as a critical reminder to apply security patches as soon as they become available.
The Akira ransomware group demonstrated the ability to bypass multi-factor authentication (MFA) on SonicWall SSL VPN devices. While the exact method is still under investigation, it is suspected that the attackers used stolen OTP seeds, highlighting that even MFA may not be foolproof against determined adversaries.
Professional services firms, legal practices, and small-to-medium businesses that use SonicWall VPNs for remote access are at extreme risk. This attack shows the need for layered security and continuous monitoring, even with MFA in place.
In a positive development, the rate of ransomware victims paying ransoms has dropped to a historic low of 23%. This trend suggests that improved backup and recovery strategies, along with stronger guidance from cyber insurance carriers and law enforcement, are making ransom payments a less viable option for businesses.
This trend is a positive sign for all industries. It reinforces the importance of investing in cyber resilience, incident response planning, and robust backup solutions rather than relying on paying ransoms.
CISA warned that a high-severity privilege escalation vulnerability in the Linux kernel is being actively exploited in ransomware attacks. This allows attackers to gain elevated privileges on Linux systems, facilitating the deployment of ransomware and making it easier to move laterally within a network.
Web hosting providers, cloud service providers, and technology companies with Linux-based data centers are at high risk. This trend highlights the growing focus of ransomware gangs on Linux infrastructure, which has traditionally been seen as more secure.
Major US telecom backbone provider Ribbon Communications was the target of a nation-state cyberattack, raising concerns about the security of the nation’s telecommunications supply chain. The potential impact of such an attack has been compared to the Colonial Pipeline incident, highlighting the systemic risk to critical infrastructure.
While the telecommunications sector is the primary target, the impact extends to all industries that depend on reliable communication services, including financial services, healthcare, and emergency services.
Microsoft took action to disrupt a Rhysida ransomware campaign that was distributing malicious Microsoft Teams installers through malvertising. The attackers used over 200 code-signing certificates to make the fake installers appear legitimate, demonstrating a sophisticated approach to supply chain attacks.
Remote-first companies and organizations with bring-your-own-device (BYOD) policies are at high risk. This incident emphasizes the need for application whitelisting and user education to prevent the installation of malicious software.
👉 Visit our website and apply for a grant today to strengthen your defenses.
Don’t wait until it’s too late. Take the first step towards a more secure future by running a Cyber Penetration Test and exploring the grant opportunities available through the Cyber Grants Alliance.